What we know so far about the Gmail data breach
Originally reported to ExpressVPN by Fowler, this publicly exposed database, made up of an enormous 96 GB of raw credential data, was not encrypted or password-protected. The 149 million+ unique logins and passwords contained in this dataset were arranged into countless publicly-accessible files.
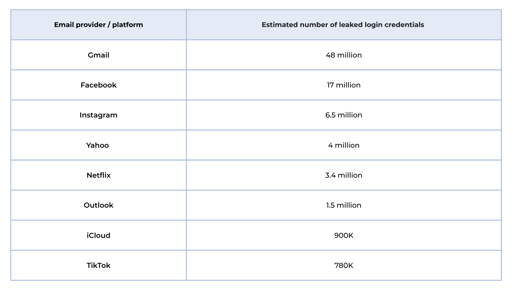
Inside the dataset were login credentials for a variety of platforms, with the biggest hitter, Gmail, having a massive 48 million accounts compromised.
Here’s a breakdown of the biggest email providers and platforms that have been affected:
Unlike other recent significant cyber attacks - such as those on Australian flag carrier Qantas, and car manufacturer Jaguar Land Rover - this data breach was not a ransomware attack perpetrated through social engineering. Rather, this database was the result of using keylogging and ‘infostealer’ malware: a type of malicious software designed to silently collect credentials from infected devices.
The stolen data was organised by victim and source, including emails, usernames, passwords, and the exact login URLs.
Gmail data breach: risks and consequences
Because this dataset included emails, usernames, passwords, and the exact login URLs, criminals could automate ‘credential-stuffing’ attacks against compromised accounts, potentially gaining access to email, financial services, social networks and more. This dramatically increases the risk of fraud and identity theft for those affected.
Fact: there's a cyber incident every 6 minutes in Australia
The Australian Government's latest Annual Cyber Threat Report revealed that they received 84,700 cybercrime reports between 2024-2025 - this averages out to one report every 6 minutes.
Despite the average cost of one cyber attack in Australia costing between $56,600 to $202,700, there is still an on-going cybersecurity skills shortage.

What this means for cyber security and data privacy in Australia and New Zealand
Data privacy can feel more difficult in 2026 than every before because the volume and reach of data collection keeps growing. As we rely more on digital services and devices, the importance of mitigating data breaches - whether miscellaneous or otherwise - is now non-negotiable.
The theme ‘take control of your data’ for Data Privacy Week 2026, highlights how individuals and organisations can make better choices to treat personal data with the care it deserves.
But the bottom line? Increasing the number of certified cybersecurity professionals is key to reducing the risk of cybercrime.
As the Asia-Pacific region experiences the highest global rate of ransomware attacks, the demand for qualified cybersecurity professionals is increasing rapidly. In turn, employers are willing to pay cyber professionals far above the national average to avoid the huge cost of a cyber attack.
Our range of courses and pathways is created to equip you with job-ready skills from globally recognised cybersecurity certification providers like CompTIA, EC-Council, and Cisco.
If you’re looking to make a career change into cybersecurity with no experience, or if you’re looking to improve your skillset to stand out in a highly lucrative career, then why not arrange a free, no-obligation call with me or one of my colleagues to see how we can support you? We’re here to answer any questions you might have about cybersecurity qualifications or our services.
Related Articles
 Cyber Security
Cyber SecurityNew Zealanders are Losing More Than $1.6 Billion Annually to Cybercrime, Government Report Finds
Backed by Microsoft, the New Zealand government’s 2026-2030 Cyber Security Strategy takes a notable step toward proper nationwide prevention of cybercrime. But does it overlook the huge demand for skilled cyber professionals in NZ?
Read More Cyber Security
Cyber SecurityReflecting on the top 5 global cyber-attacks of 2025 – the growing need for skilled cyber professionals
We take the time to reflect on some of the most news-worthy cyber-attacks, how they happened, and what it says about the global cyber skills gap.
Read More Cyber Security
Cyber SecurityWhat Is Cyber Security Asset Management?
Learn what CSAM means in cybersecurity, why asset management matters, and how it supports risk reduction, compliance, and real-world cyber roles.
Read More Cyber Security
Cyber SecurityWhat Is Spear Phishing in Cybersecurity?
Learn what spear phishing is, how targeted attacks work, and why they matter in cybersecurity. This is a clear, practical guide for those learning about common cyber attacks and defences.
Read More

